News
Definition and How It Works
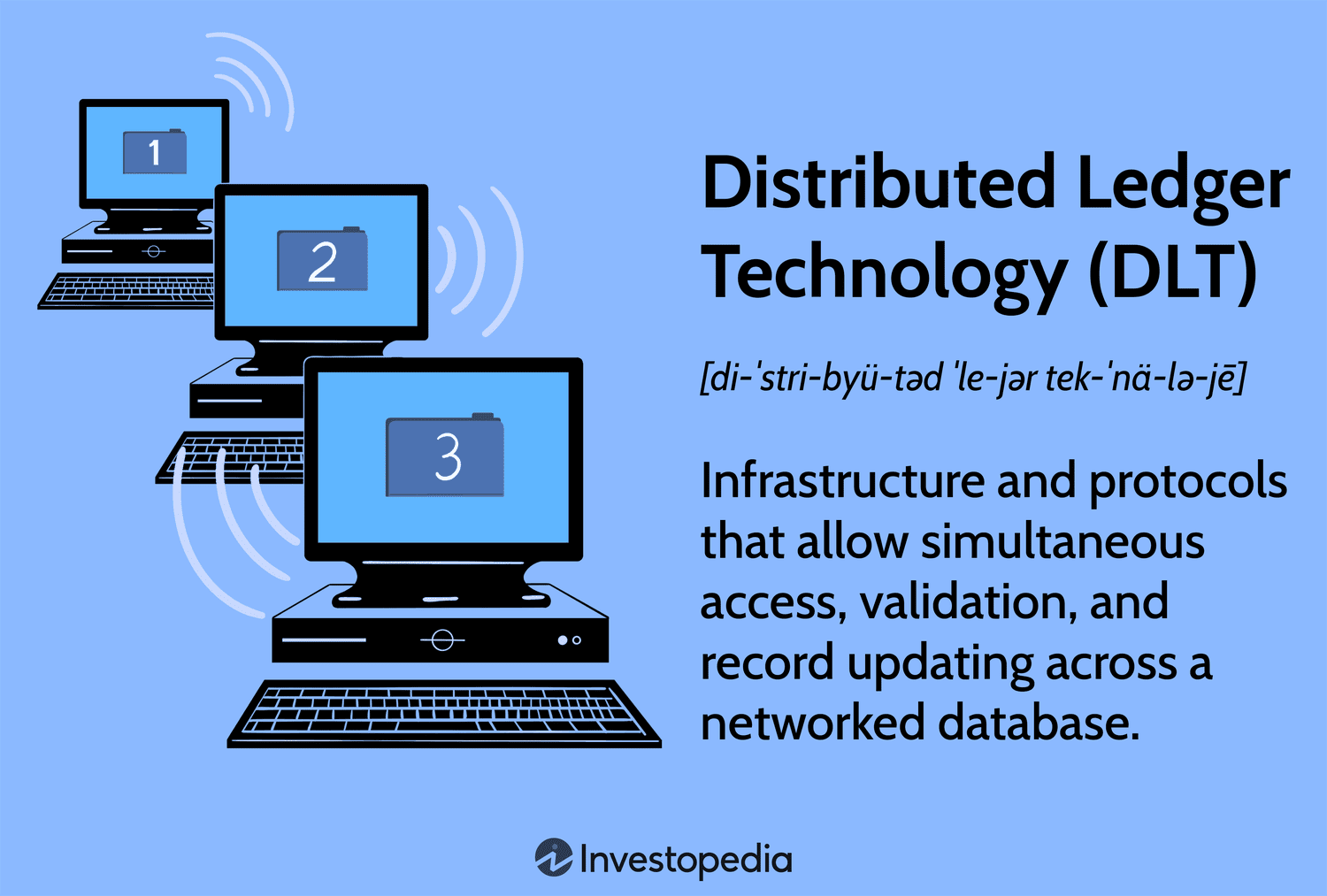
What Is Distributed Ledger Technology (DLT)?
Distributed ledger technology (DLT) is the technological infrastructure and protocols that allow simultaneous access, validation, and record updating across a networked database. DLT is the technology blockchains are created from, and the infrastructure allows users to view any changes and who made them, reduces the need to audit data, ensures data is reliable, and only provides access to those that need it.
Key Takeaways
- Distributed ledgers are maintained by a network of nodes, each of which has a copy of the ledger, validates the information, and helps reach a consensus about its accuracy.
- Distributed ledgers have been around for decades but have become more well-known, researched, used, and developed since Bitcoin was introduced.
- Distributed ledgers can be used in nearly every industry where data is collected and used.
- All blockchains are distributed ledgers, but not all distributed ledgers are blockchains.
- Though DLT enhances accountability, security, and accessibility, it is still complex and difficult to scale.
History of Distributed Ledgers
Distributed computing is not new—businesses and governments have been using the concept for several decades. In the 1990s, it became possible for multiple computers and users in different locations to solve problems and return the solutions to a central location.
Advances in data science, computing, software, hardware, and other technologies have made ledgers much more capable. Improved connectivity through intranet and internet protocols allowed for much more data to be collected, analyzed, and used. However, because there can now be many users with access to data, it is necessary to have someone verify the changes.
Computer and data scientists developed programs that reduced the need for auditing data. These programs used automation and data encryption techniques to verify database transactions or changes in a database’s state. This is called consensus—the act of automated majority agreement on transaction validity, where a transaction is simply a change made to a database’s state.
Distributed ledgers evolved into scalable and programmable platforms, as seen in Ethereum and HyperLedger, where solutions can be created to use a database, or ledger, for everything from tokenizing physical assets to streamlining manufacturing and other business processes.
How Distributed Ledger Technology Works
DLTs allow information to be stored securely and accurately using cryptography. The data can be accessed using “keys” and cryptographic signatures. Once the information is stored, it can become an immutable database; the rules of the network, written into the coding of the database programming, govern the ledger.
If something is immutable, it is unable to be changed. Distributed ledgers are only immutable if they are programmed to be that way. Blockchains are immutable because they are decentralized and cryptographically enhanced public ledgers.
Because they are decentralized, private, and encrypted, distributed ledgers are less prone to cybercrime, as all the copies stored across the network need to be attacked simultaneously for the attack to be successful. Additionally, the peer-to-peer sharing and updating of records make the whole process much faster, more effective, and cheaper.
Every device on a distributed ledger network stores a copy of the ledger. These devices are called nodes—a network can have any number of nodes. Any changes to the ledger, such as moving data from one block to another, are recorded across all nodes. Because each node has a copy of the ledger, each one publishes its version with the latest transactions.
If the network reaches a consensus about the validity of the latest ledger, the transactions are finalized, encrypted, and used as a basis for the following transactions. This is how blockchains develop—each block contains encrypted information about the proceeding block, which makes them impossible to change.
Industries Using Distributed Ledger Technology
Distributed ledgers are created for many different purposes, but one of the most used ways is as a platform for others to scale and use. One of the more well-known distributed ledgers is Hyperledger Fabric. It is a modular and scalable DLT platform several businesses have used to create solutions that span many industries. Some industries that have implemented DLT solutions include aviation, education, healthcare, insurance, manufacturing, transportation, and utilities.
Supply chains can benefit greatly from DLT. Many factors make them inefficient, inaccurate, and susceptible to corruption or losses. Fujitsu, a global data and information technology company, has designed distributed ledger technology to enhance supply chain transparency and fraud prevention by securing and tracking data.
Fujitsu’s Rice Exchange was created to trade rice, ensuring data regarding sources, prices, insurance, shipping, and settlement are recorded on the ledger. Anyone involved can look at any data and find accurate information regarding the entire process because it cannot be changed. All data is entered and secured automatically by the platform—it will eventually provide tracking information for rice shipping containers as it is shipped to its final destination.
Uses of Distributed Ledger Technology
Aside from specific industries, there are also specific situations where DLT solutions have proven to add value. Some examples of specific DLT uses include:
- Record transactions: DLT enables secure, transparent, and decentralized transactions without the need for a central authority. As DLT is a ledger, it records inputs and outputs. Though this naturally lends itself to financial records, DLT can record any type of transaction, not just financially based ones.
- Secure identities: DLT can be used to create a secure and tamper-proof digital identity for individuals, as the technology can provide a reliable way to verify identities and prevent identity theft.
- Collect votes: DLT can be used to create a secure and transparent voting system that can prevent voter fraud and ensure the integrity of the voting process. As mentioned above, as transactions (financial or non-financial) are recorded, a transparent, immutable, open ledger of interactions with users is saved. This enhances the equity and believability of a collection of opinions.
- Enter contracts: DLT allows for smart contracts, agreements that automatically execute or complete based on prevailing conditions. For example, an insurance claim may automatically release funds once the claim has been processed. This limits error and DLTs make it more difficult for precarious activity by bad actors.
- Demonstrate ownership: DLT can be used to record property transactions, creating a tamper-proof and transparent record of ownership and transfer of property. Though there are some limitations on translating real-world ownership of physical assets to a distributed ledger, the ledger may be able to convey an unchangeable source of truth regarding ownership.
DLT may also be referred to as a shared ledger as it requires a ledger to be shared across a peer-to-peer computer network.
Advantages and Disadvantages of Distributed Ledger Technology
Pros of DLT
DLT holds many benefits over more traditional centralized ledger systems. Because DLT is a decentralized system, there is no central point of control or failure. This makes DLT more resilient to attacks and less vulnerable to system-wide failures. Also, because DLT uses cryptographic algorithms to secure data, it is nearly impossible to tamper with or forge records. This enhances the trustworthiness of the data and reduces the risk of fraud.
DLT allows for transparent access to data and transactions, allowing all users greater visibility into the operations of the system. This may lead to greater buy-in from users due to transparency and accountability of records.
DLT can streamline processes by removing intermediaries and automating transactions through smart contracts. Because smart contracts may automatically execute when contract conditions are met, there may be less need for human interaction or administration. This can reduce costs and increase efficiency.
Last, DLT can enable greater financial inclusion. Some people may not have access to traditional banking services. As DLT often relies only on an internet connection, individuals who would be otherwise limited may have access to a greater range of services. This extends to the use of different platforms and networks via interoperability.
Cons of DLT
Due to DLT’s infancy, there are still considerable downsides to the technology. DLT is still complex and difficult to implement and maintain. Leveraging the solution often requires specialized knowledge and expertise, especially to implement.
DLT can struggle with scalability as the number of participants and transactions increases. As a result, DLT processes may lead to slower processing capabilities or higher use costs. In addition, some DLTs such as Bitcoin require a significant amount of energy to maintain the network and process transactions. This can have negative environmental impacts.
As seen by the actions of bad actors, the lack of regulation and standardization in the blockchain industry (blockchains are derived from DLT) can lead to risk for users and investors. By extension, DLT requires widespread adoption to be effective, and many industries and organizations may be hesitant to adopt new technologies due to these security concerns.
Distributed ledgers might be immutable, but this benefit also comes with a significant downside—if mistakes are made, they cannot be changed unless there are users with permission to do so. In a public DLT like the Bitcoin blockchain, this can be problematic. For instance, if a user typed an erroneous address in their wallet and sent the wrong person some Bitcoin, they cannot reverse the transaction.
Pros
-
Spreads systematic risk around, minimizing the risk of a single point of failure
-
Has greater security due to cryptographic algorithms
-
Allows for transparency and visibility into operations
-
May prove to be more efficient due to smart contract automation
-
Offers individuals with limited access to traditional systems potentially greater capabilities
Cons
-
Is more complex compared to traditional ledger solutions
-
Can require higher energy consumption for operation
-
May have difficult scaling as more users/transactions occur
-
Some applications remain risky due to lack of regulation
-
May prove to be difficult to reverse fraudulent or erroneous activity
Why Distribute Ledger Technology Is Important
DLT is important because it has the potential to transform how information is recorded, stored, and distributed. The importance is often cited across three pillars: security, transparency, and accessibility.
Security
Traditional ledger technology often has a central point of control, with one single entity often in charge of the ledger. DLT makes the ledger more resilient to attacks and less vulnerable to system-wide failures. As DLT uses cryptographic algorithms to secure data, it also makes it more difficult to tamper with or forge records.
Consider a traditional banking system where a banker is the central point in ensuring your transaction is recorded correctly. In contrast, consider a DLT solution built on a consensus mechanism where all distributed ledgers must be in agreement about how a transaction is recorded. This validation of transactions allows greater trust among users and removes the power an individual might have to alter data.
Transparency
Centralized, traditional ledgers often restrict access to specific individuals. Though this still holds value for sensitive information, there are many use cases where it is more beneficial for all when data and information are broadly distributed and transparent. Consider the example above of voting; having digitally distributed, undisputable, verifiable records of voting may enhance the believability of results.
DLT is also important as it holds the theory of reducing fraud and increasing accountability in the long term. Note how all transactions within a DLT system are able to be viewed by anyone with access to the DLT. The information may be “audited” by anyone at any time, potentially demotivating bad actors from entering into nefarious activity in such a public sphere.
Accessibility
Last, DLT may eventually be critically important to developing and emerging countries or regions where centralized technologies are limited. Think about the banking limitations of different countries around the world. DLT boasts the ability to store and record transactions using only a network connection as opposed to a very niche (and expensive) connection, such as a bank account at a specific bank.
As DLT is a relatively new technology that is still being explored and developed, this presents opportunities for innovation and the creation of new applications and use cases. In general, because of the ease of being to access DLT solutions, there are many positive implications on the broad public being able to communally access a shared network with often fewer bureaucratic hurdles to meet prior to access.
Distributed Ledger Technology Consensus Mechanisms
A central facet of DLT is how transactions are “approved” when consensus needs to be reached among a disparate user base. Without a universally-agreed system of how items are accepted within the DLT, users of the DLT would be unable to universally agree on how items to include and what items should be excluded.
This process of reviewing transactions is called a consensus mechanism, and a DLT may leverage any of the following processes. Note that consensus mechanisms are constantly evolving, and only several of the more common approaches are listed below:
- Proof of Work (PoW): In PoW, miners compete to solve cryptographic puzzles to validate transactions and create new blocks. This type of consensus mechanism requires computational power, making it a less environmentally friendly method. The concept behind PoW is that miners must financially invest and commit resources to approve transactions, so they are incentivized to be “good actors.”
- Proof of Stake (PoS): In PoS, validators hold a stake in the network and are chosen to validate transactions based on the amount of the stake they hold. Seen as a more environmentally friendly option, it is very expensive to become a full validator and earn rewards.
- Delegated Proof of Stake (DPoS): DPoS is a variant of proof of stake where the network selects a limited number of validators to validate transactions. This variation reduces the computational resources required to secure the network. In many ways, a DPoS system is seen as a more democratic means of selecting approvers and, in some instances, might offer better scalability.
Distributed Ledgers vs. Blockchain
There are several key factors that distinguish blockchain from distributed ledgers. In general, blockchain is a specific type of DLT. DLTs may take various forms, while a blockchain uses one specific infrastructure that uses a linear system of blocks to record and verify information.
Blockchains often leverage a proof of work or proof of stake consensus mechanism, whereas a DLT has a much broader range of mechanisms available. In addition, DLTs are often more broadly used across industries as they can be leveraged for broader problems. Blockchain has historically been most associated with the financial sector as a means of recording a payment system. The security behind either may also vary, with blockchain having a very defined set of criteria within the DLT realm.
Blockchain
-
Data is stored in chained files called “blocks”
-
Always encrypted
-
Generally public and permissionless, but some are permissioned
-
Always immutable
What Is Another Word For Distributed Ledger?
You might hear a distributed ledger called a share ledger.
Are DLT and Blockchain the Same?
All blockchains are distributed ledgers (DLs), but the opposite is not true—blockchains are derived from DLs.
What Is the Difference Between a Distibuted Ledger and a Centralized Ledger?
A centralized ledger is a database stored in a centralized location. It could be hosted by an individual, group, or organization that maintains it. A distributed ledger is a database where a copy is distributed, shared, and automatically synchronized.
What Is Meaning of DLT?
Distributed ledger technology is the concept of using modern networking systems, hardware, and programming to distribute copies of a database to multiple nodes that synchronize it to maintain it.
The Bottom Line
Distributed ledger technology uses databases stored on separate, connected devices in a network to ensure data accuracy and security. Blockchains evolved from distributed ledgers to address growing concerns that too many third parties are involved in too many transactions.
Distributed ledger technology is becoming necessary in modern businesses and enterprises that need to ensure accuracy in financial reporting, manage supply chains, prevent fraud, and identify inefficiencies. It has many more use cases in time-consuming and costly business activities.
News
Blockchain Technology Will Transform Water Access and Management Globally

Disclosure: The views and opinions expressed here are solely those of the author and do not represent the views and opinions of the crypto.news editorial team.
Access to clean water is a basic human need, yet billions of people around the world still struggle to get it. According to the World Health Organization, over 2 billion people live in countries suffering from severe water stress, and this number is expected to continue to grow due to climate change and population growth.
Traditional water management systems have struggled to address these challenges, often hampered by inefficiencies, lack of transparency, and misallocation of resources. Blockchain technology offers a promising solution to these challenges, providing equitable access and sustainable use of this crucial resource.
The current state of water management
Water management today faces several pressing issues. Inefficiencies in water supply, distribution, and use, coupled with a lack of real-time monitoring, often result in resource waste and misallocation. Many water sources fail to realize their full potential due to infrastructure and financing shortfalls. For example, the Environmental Protection Agency (EPA) report indicated that the United States would need to invest $625 billion over the next 20 years to repair, maintain and improve the country’s drinking water infrastructure due to aging pipes and other infrastructure problems. Additionally, in the United States alone, household leaks can to waste nearly 900 billion gallons of water per year nationwide. This is equivalent to the annual domestic water consumption of nearly 11 million homes.
Furthermore, corruption and mismanagement of water resources can cause unequal distribution, with disadvantaged communities often bearing the brunt of water scarcity. For example, South Africa is struggling with myriad challenges to its water security: drought, inadequate water conservation measures, outdated infrastructure, and unequal access to water resources. The country faces significant water scarcity, with demand expected to outstrip supply by 2030, creating a projected gap of 17%.
Furthermore, the global water industry is highly monopolized, with a few key players controlling a significant share of the market. These companies exert substantial influence over the water supply chain, often prioritizing profit over equitable distribution and environmental responsibility. This concentration of power can lead to inflated prices and limited access for vulnerable populations. The global bottled water market alone is projected to reach $509.18 billion by 2030, with these large companies capturing a significant share of revenue. This monopolization exacerbates existing inequalities in water access and highlights the need for more decentralized and community-driven water management solutions.
Source: Grand View Search
The potential of blockchain in water management
Blockchain technology can address these issues by providing a transparent, secure, and decentralized platform for water resource management. This approach offers several advantages:
- Transparency and accountability. Blockchain’s immutable ledger ensures that all transactions and data entries are transparent and cannot be changed once recorded. This transparency can reduce corruption and ensure that water resources are allocated fairly and efficiently. For example, blockchain can be used to track water usage from source to end user, providing a clear record of how water is distributed and used. This level of transparency can help hold authorities accountable and manage water resources sustainably.
- Efficient resource management. Blockchain can facilitate the creation of smart contracts, which are self-executing contracts with the terms of the agreement written directly into the code. These contracts can automate water distribution based on real-time data, directing water to where it is needed most. For example, smart contracts could be used to manage urban water supply systems, automatically adjusting water distribution based on real-time consumption patterns and demand. This can help optimize water use, reduce waste, and ensure that households and businesses receive the right amount of water at the right time.
In Dubai, the Dubai Electricity and Water Authority (DEWA) has implemented a blockchain-based smart water network initiative as part of its broader smart city strategy. This project integrates blockchain technology with IoT sensors to monitor water usage in real time, manage distribution, and detect leaks. The decentralized ledger ensures data integrity and transparency, enabling more efficient water management and reduced waste. DEWA’s initiative aims to improve sustainability and resource management in the rapidly growing city, highlighting the potential of blockchain to support urban water management and conservation efforts.
Community participation and ownership
Through blockchain, individuals can directly control and monetize their access to water resources, eliminating the need for third-party intermediaries. This direct control model allows local communities to make collective and transparent decisions about their water use. By managing their water directly from the source, communities can tailor water management practices to their specific needs, promoting equitable distribution and encouraging a sense of accountability and stewardship.
Additionally, future models could allow people to monetize their access to water through web3 technologies. For example, a community-to-business (C2B) model could allow people to sell water directly to companies. In this model, people do not have to own the water directly, but can profit by staking their tokens during event sales pools. This approach not only supports sustainable water management, but also creates economic opportunities for community members. Additionally, a “Burn to Secure” protocol can be used to provide water allocation rights. This protocol provides a true sense of water security and financial opportunity by allowing people to redeem their rights. This system not only secures future water allocations, but also increases token scarcity and value.
Additionally, a pure sense of investment is achieved through investments in water sources. This leads to potential financial returns and dividends by addressing the inefficiencies in water supply mentioned above. By investing to finance infrastructure projects, such as building factories and improving distribution systems, more water can be brought to communities, creating additional economic opportunities.
Monetizing water access through the C2B model, the “Burn to Secure” protocol, and investments in water sources all generate economic benefits for the community, promoting a more equitable and efficient water management system.
Overcoming challenges
While blockchain technology has the potential to improve water management, there are challenges to its adoption. The complexity of blockchain systems and the need for technological infrastructure can be barriers, especially in developing regions. Additionally, there are concerns about the significant energy consumption of blockchain networks. However, technological advances and the development of more energy-efficient blockchain solutions are helping to alleviate these concerns. Additionally, education and capacity building are key to ensuring stakeholders understand how to effectively use blockchain technology. Governments, NGOs, and private sector partners need to work together to provide training and support to communities and water management authorities.
Blockchain technology offers a practical and effective means to improve water management. In addition to addressing inefficiencies, blockchain empowers communities, promotes sustainable practices, and opens up new economic opportunities through models like community-to-business (C2B). As we face the growing challenges of climate change and population growth, blockchain is not only an innovative solution, but represents a fundamental shift in the way we manage and value water resources. Adopting blockchain in water management is essential to creating a sustainable and equitable future by changing the way we interact with and protect our most vital resource.

Jean-Hugues Gavarini
Jean-Hugues Gavarini is the CEO and co-founder of LAKE (LAK3), a real-world asset company leveraging blockchain technology to decentralize access to the global water economy. LAKE aims to ensure access to clean water for all, protect water resources, and deliver water to those in need through innovative technologies. Jean-Hugues has a diverse career spanning the luxury, fashion, and footwear industries. His career path includes notable successes at Mellow Yellow, Cremieux, and Tod’s. Raised between Silicon Valley and the French Alps, Jean-Hugues has always been immersed in technology and freshwater resources. In 2018, Jean became the CEO of Lanikea Waters, a water solutions entity based in the French Alps. In 2019, the concept of LAKE was born, embodying his commitment to innovation and sustainability.
News
Blockchain and AI Expo 2024

With rapid advances in the world of AI and blockchain, there are opportunities to leverage the security and transparency features of blockchain to improve the reliability and trust of AI systems and data transactions.
Explore the synergy of these advanced technologies in virtual mode Blockchain and AI Expowhich takes place on October 31, 2024 TO 10:00 GMT.
The event features cutting-edge presentations led by leading experts in evolving fields. Presentations are set to explore opportunities and challenges in the fusion of blockchain and AI, real-world applications, ethics, innovations in environmental sustainability, and more!
Gain a comprehensive understanding of how these technologies can synergistically drive innovation, optimize operations, and promote strategic growth opportunities. Develop your knowledge to facilitate informed decision making and give your company a competitive edge in the growing technology landscape.
News
Nigeria Eyes National Blockchain Nigerium for Data Sovereignty

Nigeria is keeping an eye on a new native blockchain network to protect the country’s data sovereignty.
According to local media, a team from the University of Hertfordshire has proposed the new blockchain, Nigeriato the National Information Technology Development Agency (NITDA).
Chanu Kuppuswamy, who leads the team, argued that relying on blockchain networks whose developers are located in other regions poses national security risks to the Nigerian government. He further said that Nigerium would allow the West African nation to customize the network to meet specific needs, while also promoting data sovereignty.
In his presentation, Chanu cited the recent migration of Ethereum to test of participation (PoS) consensus as an instance in which no Nigerians were involved but whose impact is far-reaching.
“Developing an indigenous blockchain like Nigerium is a significant step towards achieving data sovereignty and promoting trust in digital transactions in Nigeria,” he said.
While receiving the proposals in Abuja, NITDA’s Kashifu Abdullahi acknowledged the benefits a local blockchain would bring to Nigeria, including increased security of citizens’ data.
However, a NITDA spokesperson later clarified that Nigerium is still at the proposal stage and that the government has not yet decided whether to proceed or not.
“The committee is still discussing the possibility with stakeholders. Even if a decision is finally made, there is no guarantee that the name will be Nigerium,” the spokesperson told the media.
Nigerium’s reception in the country has been mixed. Some, like financial analyst Olumide Adesina, To say the network is “dead on arrival”. He believes the Nigerian government’s poor record in following through on its big technology plans will claim another victim. He pointed to the eNaira as a missed opportunity whose chances of success were much higher than those of Nigerium.
Others welcomed the proposal. Chimezie Chuta, who chairs the renewed The Nigerian Blockchain Policy Committee is “extremely optimistic“that Nigerium will be more successful than eNaira.
Speaking to a local news agency, Chuta stressed that eNaira failed because the central bank initiated the project on its own, without involving any stakeholders.
“They just cooked it and expected everyone to like it. [With Nigerium]there will be a lot of collaboration,” he said.
Registration of property title, digital identity and Certificate Verification are among the use cases that Nigerium is expected to initially target. However, Nigeria has already made progress in some of these fields through public blockchains.
SPPG, a leading school in governance and politics, announced in May the country’s first blockchain certificate verification system. Built on the The BSV BlockchainIt was developed in collaboration with the blockchain data recording company VX Technologies and local lender Sterling Bank.
Watch: The Future Has Already Arrived in Nigeria
 Italian: https://www.youtube.com/watch?v=M40GXUUauLU width=”560″ height=”315″ frameborder=”0″ allowfullscreen=”allowfullscreen”>
Italian: https://www.youtube.com/watch?v=M40GXUUauLU width=”560″ height=”315″ frameborder=”0″ allowfullscreen=”allowfullscreen”>
New to blockchain? Check out CoinGeek Blockchain for Beginners section, the definitive guide to learn more about blockchain technology.
News
Cambodian CBDC Developer to Build Palau Bond Market on Blockchain: Report
A Japanese fintech developer will build a blockchain-based bond market gateway for Palau, aiming to launch a trial in 2024 and a full launch the following year.
Japanese fintech developer Suramitsubest known for developing a central bank digital currency (CBDC) for Cambodia, is intended to build a Blockchain-gateway to the bond market based on the Pacific island nation of Palau, Nikkei He learned.
Soramitsu won the contract and plans to introduce the market on a trial basis in fiscal 2024, with a full launch scheduled for the following year, allowing the Palauan government to issue bonds to individual investors and efficiently manage principal and interest payments, according to the report.
The total cost of the project is estimated at several hundred million yen ($1.2 million to $5.6 million), less than half the cost of a non-blockchain alternative, people familiar with the matter said. The project has reportedly received support from Japan’s Ministry of Economy, Trade and Industry, with Japan’s foreign and finance ministries providing strategic and management advice on the project.
Soramitsu’s successful development of Cambodia’s CBDC in 2020 has boosted its reputation, with the digital currency’s popularity soaring, with over 10 million accounts opened by December 2023, representing 60% of Cambodia’s population. Following this, Cambodia’s central bank governor Chea Serey indicated intends to expand the reach of its CBDC internationally, particularly through collaboration with UnionPay International, the Chinese card payment service, and other global partners.
While Soramitsu’s work in Cambodia has been well received, the long-term popularity of CBDCs remains to be seen. As of late June, crypto.news reported a sharp drop in activity in India’s digital currency, the e-rupee, after local banks stopped artificially inflating its values.
According to people familiar with the matter, the Reserve Bank of India managed to hit the 1 million retail transaction milestone last December only after the metrics were artificially infiltrated by local banks, which offered incentives to retail users and paid a portion of the bank’s employees’ salaries using the digital currency.
-

 News1 year ago
News1 year ago“Captain Tsubasa – RIVALS” launches on Oasys Blockchain
-

 Ethereum1 year ago
Ethereum1 year agoComment deux frères auraient dérobé 25 millions de dollars lors d’un braquage d’Ethereum de 12 secondes • The Register
-

 News1 year ago
News1 year agoSolana ranks the fastest blockchain in the world, surpassing Ethereum, Polygon ⋆ ZyCrypto
-

 Videos1 year ago
Videos1 year agoHistoric steps for US cryptocurrencies! With a shocking majority vote!🚨
-

 Videos1 year ago
Videos1 year agoIs Emorya the next gem💎 of this Bitcoin bull run?
-

 News1 year ago
News1 year agoSolana Surpasses Ethereum and Polygon as the Fastest Blockchain ⋆ ZyCrypto
-

 Videos1 year ago
Videos1 year agoNexus Chain – Ethereum L2 with the GREATEST Potential?
-
 News1 year ago
News1 year agoFnality, HQLAᵡ aims to launch blockchain intraday repositories this year – Ledger Insights
-

 Ethereum1 year ago
Ethereum1 year agoScaling Ethereum with L2s damaged its Tokenomics. Is it possible to repair it?
-

 Regulation1 year ago
Regulation1 year agoFinancial Intelligence Unit imposes ₹18.82 crore fine on cryptocurrency exchange Binance for violating anti-money laundering norms
-

 Bitcoin1 year ago
Bitcoin1 year agoBitcoin Drops to $60K, Threatening to Derail Prices of Ether, Solana, XRP, Dogecoin, and Shiba Inu ⋆ ZyCrypto
-

 News1 year ago
News1 year agoSendBlocks Debuts with Major Support to Improve Blockchain Data Management










