News
Blockchain Intelligence to Investigate Crypto Crime

With a global market capitalization exceeding $2 trillion, regulation increasing worldwide, and adoption growing each year, cryptocurrency is here to stay. What does this mean for law enforcement?
It’s no surprise that where economic opportunity abounds, so do attempts to subvert it with crime. Much like fiat currency, crypto has been used in connection with scams, ransomware, money laundering, child exploitation, terrorist financing, sanctions evasion, and darknet market commerce. In 2023, $24.2 billion of total crypto transaction volume was tied to illicit activity. While this is a large figure, without context, it doesn’t quantify the human toll of crypto-related crime.
For example, one insidious crime with a crypto nexus — “pig butchering” — is a unique social engineering scam in which scammers build trust with victims via social media apps and text messages, and trick them into investing their money on fake platforms. The impact of these scams has been devastating, with some victims losing pensions and lifetime savings, along with their peace of mind and confidence.
Pig butchering scams are just one example of how criminals have been adapting their tactics with increasing sophistication in the last few years. Now more than ever, law enforcement must be equipped with the knowledge and capabilities to combat crypto crime. This blog post will discuss how criminals are using crypto and why, and how law enforcement agencies both large and small leverage blockchain intelligence to investigate crypto-related crime.
How crypto and crime intersect
Cryptocurrencies have criminal relevance due to their versatility as both a means of payment and an investment vehicle, and are appreciated for their pseudonymity. Cryptocurrency is often employed in darknet trading, ransomware attacks, forms of hacking like cryptojacking — in which criminals secretly use victims’ computing power to mine crypto — and money laundering. In 2023, over $22 billion in crypto worldwide was used for that purpose. Crypto is also used in various types of fraud, and has been associated with theft via hacking incidents, as well as facilitating CSAM (child sexual abuse material), sanctions evasion, terrorist financing, and commercial offenses (e.g., weapons dealing, counterfeiting money, forged documents, and the sale of narcotics and medicine).
Here are some of crypto’s attributes and capabilities that make it desirable for criminal use:
- Pseudonymity: Some criminals mistakenly perceive crypto as anonymous, when it’s actually pseudonymous because crypto exchanges are required to maintain customer information in order to comply with know your customer (KYC) and anti-money laundering (AML) regulations. Still, a crypto transaction on a blockchain ledger is only initially identifiable by a public address, and finding the person or entity who controls that address takes some footwork.
- Speed, cost, and ease of use: Crypto transactions, including those made across borders, are faster and far less expensive than a standard wire transfer, in addition to being pseudonymous.
- Deception tactics: Criminals attempting to launder funds are often drawn to crypto mixers, services that obfuscate the origin and destination of crypto transactions.
- Potential return on investment: Again, crypto poses an attractive investment opportunity for some criminals, especially since it’s not tied to traditional financial markets.
Leveraging blockchain intelligence to investigate crypto crime
While the blockchain is transparent, it’s hard to read. Consider also, that the Bitcoin blockchain alone has processed nearly one billion transactions. When it comes to efficiently and effectively investigating crypto crime, blockchain intelligence provides a game-changing advantage for law enforcement as it offers the ability to analyze extensive on-chain datasets, graphing capabilities to organize that data, and contextualized insight into illicit crypto activity. By contrast, anyone can search for crypto transactions using a block explorer, but those tools don’t aggregate data in actionable ways.
The image above shows a single transaction as displayed on a block explorer. That data shown above may be public, but it’s not very insightful; it begs more questions than it answers. For example:
- Who are the pseudonymous entities? Are they cryptocurrency exchanges, merchant processors, or darknet markets?
- Why are they transacting? Is it a payment, an investment, or a smart contract?
- How much value are they transacting? Is it hundreds, thousands, or millions of dollars worth of cryptocurrency?
Blockchain intelligence helps organizations answer these questions. Using it, law enforcement agencies identify criminal entities by examining on-chain activity like the movement of stolen or laundered crypto. The teams that support this technology cultivate extensive on-chain datasets and offer graphing capabilities that help law enforcement visually trace the flow of funds over time, and connect crypto transactions to real-world entities. These platforms also provide contextual information that facilitates a greater understanding of illicit on-chain activity. The Chainalysis graph below displays multiple, contextualized crypto transactions and the entities that initiated them.
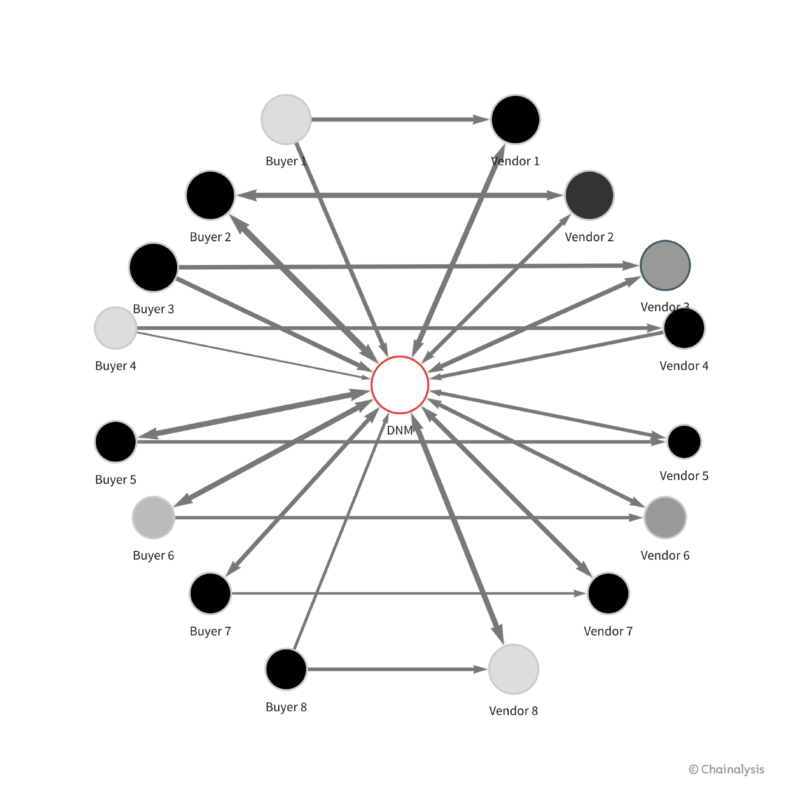
Blockchain intelligence helps investigators map crypto transactions and present them in an easily digestible format. For example, the graph above shows the transaction relationships between eight drug buyers and vendors, each of which have ties to the same darknet market. Blockchain intelligence helps law enforcement progress investigations, apprehend criminals, present cases for prosecution, and prepare the way for the seizure and recovery of crypto funds to victims when possible.
In the course of an investigation, blockchain intelligence also facilitates faster and more effective collaboration between law enforcement departments as well as government agencies. Using the same dataset contributes to a shared understanding, which drives better investigative outcomes. And while blockchain intelligence is useful for fighting crime, it can also help law enforcement be proactive in preventing crime, too. It’s possible to detect illicit activity early on by analyzing on-chain transaction patterns and relationships that could be indicative of criminal behavior. Here are some examples:
- Observing an unusual increase in transaction volumes or patterns commonly associated with money laundering or fraud
- Disrupting criminal networks by mapping the financial flows of criminal organizations, which could hinder their operations and prevent future crime
- Targeting darknet marketplaces. Proactive transaction monitoring linked to known darknet markets allows law enforcement to gather intelligence on buyers and sellers, identify emerging threats, and take action before illicit transactions escalate.
A holistic approach to tackling crypto crime
1. Prepare: Building a foundation for crypto crime response
For local governments wanting to tackle crypto crime investigations, establishing a comprehensive knowledge base across all teams and departments is critical. This shared understanding enables seamless collaboration and communication throughout an organization and across agencies, from field officers to judges.
In building a foundation to begin fighting crypto crime, leadership support for these initiatives is crucial, necessitating a commitment to capacity building and ongoing training to keep abreast of trends and develop effective policy-making, regulation, and operational strategies.
Building a community of dedicated experts is essential, too. Erin West, Deputy District Attorney for Santa Clara County, who has extensive experience with pig butchering cases says, “you need a lot of partners. This is not something that one investigator can do by themself. You need private partners, you need public partners, you need local law enforcement. You need federal law enforcement, and the idea of putting together task forces, smaller task forces nationwide, I think is a great way to tackle this.”
2. Prevent: Identifying and disrupting crypto crimes
Recognizing the use of cryptocurrency in criminal activities can be pivotal to modern investigative techniques. Agencies must enhance their ability to detect and understand crypto-related activities crucial for uncovering illicit patterns, analyzing the flow of these funds, and supporting broader blockchain investigations or policy-making. Staying informed about criminals’ evolving tactics, such as asset laundering, requires the latest technological and investigative methods.
Understanding the leverage points of crypto in criminal activities — including on/off ramps and digital wallets like CashApp — and tracing these elements through tools like government databases is essential for effective crime prevention. Disrupting crypto crime hinges on continuously updated, reliable data, and law enforcement must have access to current, accurate information.
3. Pursue: Actively chasing down offenders and recovering illicit gains
Law enforcement agencies are encountering crypto in their investigations more frequently. When these assets are discovered, they should be seized and stored until they can be investigated, and ultimately, sold for fiat money.
When it comes to stolen funds, crypto is more recoverable than many law enforcement agencies might think. Partnerships with district attorney’s offices are vital, as they place a significant role in deciding which cases to pursue towards recovering stolen funds.
Recovering crypto funds through seizure is also a technical process that demands proficiency in using seed phrases to gain access to a wallet, and conducting manual verifications to link associated wallets and assess balances. Simply put, identifying the opportunity to seize assets is complex, and the stakes have never been higher. This underscores the necessity for specialized skills and frontline training in identifying and handling critical crypto evidence, as crypto artifacts can often be discovered during search of cars, devices, premises, or when making arrests.
The U.K.’s Metropolitan Police significant Bitcoin seizure of over £2 billion in March 2024 exemplifies the potential success of these operations. This event, along with notable seizures from the past few years, underscores the global scale of the challenge and critical impact of skilled interventions.
| Hezbollah and Iran Quds Force seizure, June 2023: In the first Hezbollah-related digital currency seizure, Israeli authorities recovered roughly $1.7 million in crypto from Hezbollah, a heavily sanctioned terrorist group based in Lebanon, and from Iran’s Quds Force, which funds and works extensively with Hezbollah. Learn more.
ChipMixer seizure, March 2023: Supported by Europol, a group of international authorities seized over €40 million from this unlicensed cryptocurrency mixer. Learn more. Bitzlato seizure, January 2023: Europol seized over $19 million in crypto after the exchange’s founder was charged with money laundering. Learn more. Ronin Bridge hack recovery, September 2022: Law enforcement seized $30 million in crypto stolen by North Korean-linked hackers, the first time that crypto stolen by a North Korean hacking group was recovered. Learn more. Bitfinex hack recovery, February 2022: The IRS Criminal Investigation division, the FBI, and Homeland Security Investigations recovered $3.6 billion in crypto (the largest ever recovery of assets from a theft) in connection with the 2016 Bitfinex hack. Learn more. Silk Road hack recovery, November 2021: Law enforcement seized over $3.36 billion in cryptocurrency from James Zhong, who stole Bitcoin from the Silk Road darknet marketplace in 2012. Learn more. International money laundering operation seizure, July 2021: In June and July, British police seized a total of £294 million in cryptocurrency tied to an international money laundering investigation. Learn more. Silk Road hack recovery, November 2020: The U.S. DOJ seized $1 billion in Bitcoin from cryptocurrency from a wallet tied to a Silk Road hacker known as Individual X. Learn more. |
4. Protect: United front against crypto crime
Ultimately, successfully combating crypto crime requires a unified effort from government institutions, law enforcement, and legislators. They play an essential role in developing, implementing, and enforcing crypto policies and regulations related to cryptocurrencies and blockchain technology. This united approach is key to creating a secure yet innovative environment that keeps pace with the rapid developments of digital assets and blockchain technology.
Central to law enforcement’s arsenal against crypto crime is the sharing of blockchain intelligence across agencies. Such inter-agency collaboration, coupled with strategic public-private partnerships, strengthens regulatory frameworks and enhances compliance monitoring, thus playing an important role in crime deterrence and prevention.
Much like traditional financial investigations are a routine law enforcement responsibility, cryptocurrency investigations will need to become the same. By utilizing blockchain intelligence, government agencies can actively monitor crypto transactions. This proactive monitoring can aid crime prevention and ensure agencies are ready to respond to significant events in the financial ecosystem — like the sanctioning of major entities or the collapse of a blockchain — that could affect financial stability or pose systemic risks.
Adopting this proactive approach, backed by robust regulatory oversight, is crucial for upholding the integrity and safety of the crypto ecosystem. It highlights the importance of regulation and law enforcement in protecting against the threats posed by crypto-enabled crimes.
Gain a strategic advantage in fighting crypto crime
Over the years, we’ve seen many law enforcement agencies run successful crypto crime investigations using blockchain intelligence — everything from disrupting national security threats to protecting local communities from fraud. Blockchain intelligence plays a critical role in combating these crimes. With the increasing regulation of cryptocurrencies by governments and the continued growth in digital currency adoption, the imperative to address crypto-enabled criminal activities will only intensify. Learn how you can gain a strategic advantage in your efforts against crypto crime with blockchain intelligence.
News
An enhanced consensus algorithm for blockchain
The introduction of the link and reputation evaluation concepts aims to improve the stability and security of the consensus mechanism, decrease the likelihood of malicious nodes joining the consensus, and increase the reliability of the selected consensus nodes.
The link model structure based on joint action
Through the LINK between nodes, all the LINK nodes engage in consistent activities during the operation of the consensus mechanism. The reputation evaluation mechanism evaluates the trustworthiness of nodes based on their historical activity status throughout the entire blockchain. The essence of LINK is to drive inactive nodes to participate in system activities through active nodes. During the stage of selecting leader nodes, nodes are selected through self-recommendation, and the reputation evaluation of candidate nodes and their LINK nodes must be qualified. The top 5 nodes of the total nodes are elected as leader nodes through voting, and the nodes in their LINK status are candidate nodes. In the event that the leader node goes down, the responsibility of the leader node is transferred to the nodes in its LINK through the view-change. The LINK connection algorithm used in this study is shown in Table 2, where LINKm is the linked group and LINKP is the percentage of linked nodes.
Table 2 LINK connection algorithm.
Node type
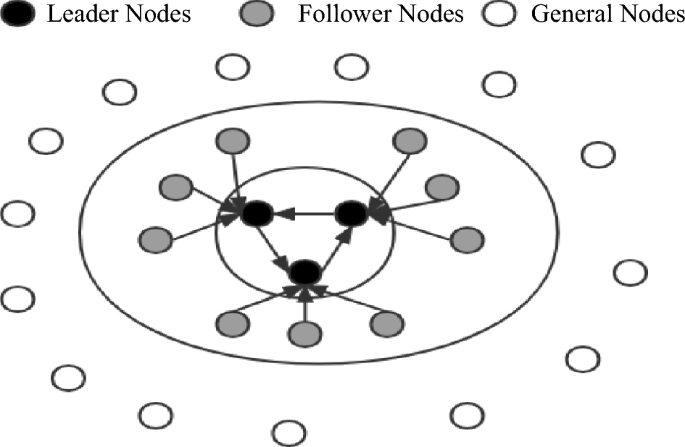
This paper presents a classification of nodes in a blockchain system based on their functionalities. The nodes are divided into three categories: leader nodes (LNs), follower nodes (FNs), and general nodes (Ns). The leader nodes (LNs) are responsible for producing blocks and are elected through voting by general nodes. The follower nodes (FNs) are nodes that are linked to leader nodes (LNs) through the LINK mechanism and are responsible for validating blocks. General nodes (N) have the ability to broadcast and disseminate information, participate in elections, and vote. The primary purpose of the LINK mechanism is to act in combination. When nodes are in the LINK, there is a distinction between the master and slave nodes, and there is a limit to the number of nodes in the LINK group (NP = {n1, nf1, nf2 ……,nfn}). As the largest proportion of nodes in the system, general nodes (N) have the right to vote and be elected. In contrast, leader nodes (LNs) and follower nodes (FNs) do not possess this right. This rule reduces the likelihood of a single node dominating the block. When the system needs to change its fundamental settings due to an increase in the number of nodes or transaction volume, a specific number of current leader nodes and candidate nodes need to vote for a reset. Subsequently, general nodes need to vote to confirm this. When both confirmations are successful, the new basic settings are used in the next cycle of the system process. This dual confirmation setting ensures the fairness of the blockchain to a considerable extent. It also ensures that the majority holds the ultimate decision-making power, thereby avoiding the phenomenon of a small number of nodes completely controlling the system.
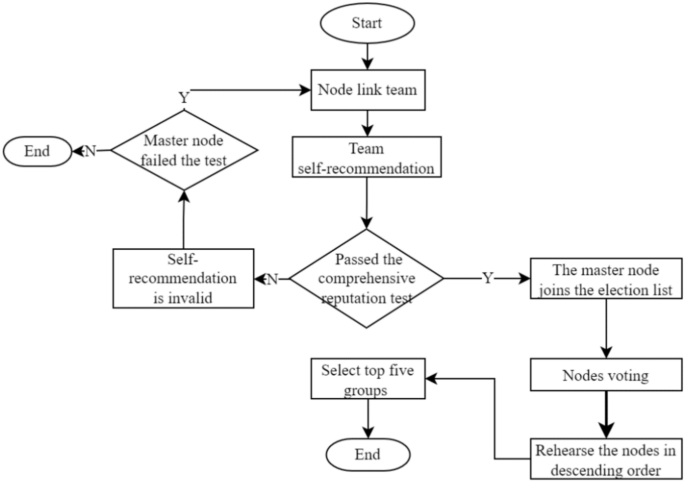
After the completion of a governance cycle, the blockchain network will conduct a fresh election for the leader and follower nodes. As only general nodes possess the privilege to participate in the election process, the previous consortium of leader and follower nodes will lose their authorization. In the current cycle, they will solely retain broadcasting and receiving permissions for block information, while their corresponding incentives will also decrease. A diagram illustrating the node status can be found in Fig. 1.
Election method
The election method adopts the node self-nomination mode. If a node wants to participate in an election, it must form a node group with one master and three slaves. One master node group and three slave node groups are inferred based on experience in this paper; these groups can balance efficiency and security and are suitable for other project collaborations. The successfully elected node joins the leader node set, and its slave nodes enter the follower node set. Considering the network situation, the maximum threshold for producing a block is set to 1 s. If the block fails to be successfully generated within the specified time, it is regarded as a disconnected state, and its reputation score is deducted. The node is skipped, and in severe cases, a view transformation is performed, switching from the master node to the slave node and inheriting its leader’s rights in the next round of block generation. Although the nodes that become leaders are high-reputation nodes, they still have the possibility of misconduct. If a node engages in misconduct, its activity will be immediately stopped, its comprehensive reputation score will be lowered, it will be disqualified from participating in the next election, and its equity will be reduced by 30%. The election process is shown in Fig. 2.
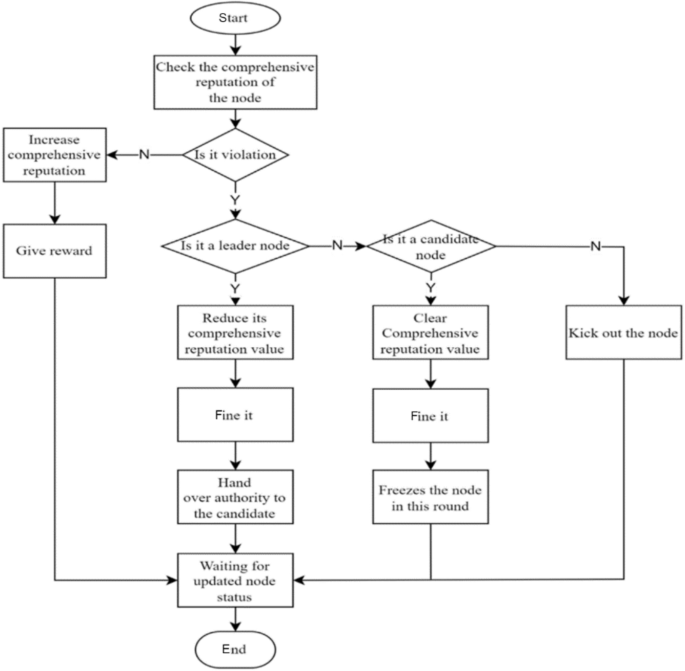
Incentives and penalties
To balance the rewards between leader nodes and ordinary nodes and prevent a large income gap, two incentive/penalty methods will be employed. First, as the number of network nodes and transaction volume increase, more active nodes with significant stakes emerge. After a prolonged period of running the blockchain, there will inevitably be significant class distinctions, and ordinary nodes will not be able to win in the election without special circumstances. To address this issue, this paper proposes that rewards be reduced for nodes with stakes exceeding a certain threshold, with the reduction rate increasing linearly until it reaches zero. Second, in the event that a leader or follower node violates the consensus process, such as by producing a block out of order or being unresponsive for an extended period, penalties will be imposed. The violation handling process is illustrated in Fig. 3.
Violation handling process.
Comprehensive reputation evaluation and election mechanism based on historical transactions
This paper reveals that the core of the DPoS consensus mechanism is the election process. If a blockchain is to run stably for a long time, it is essential to consider a reasonable election method. This paper proposes a comprehensive reputation evaluation election mechanism based on historical records. The mechanism considers the performance indicators of nodes in three dimensions: production rate, tokens, and validity. Additionally, their historical records are considered, particularly whether or not the nodes have engaged in malicious behavior. For example, nodes that have ever been malicious will receive low scores during the election process unless their overall quality is exceptionally high and they have considerable support from other nodes. Only in this case can such a node be eligible for election or become a leader node. The comprehensive reputation score is the node’s self-evaluation score, and the committee size does not affect the computational complexity.
Moreover, the comprehensive reputation evaluation proposed in this paper not only is a threshold required for node election but also converts the evaluation into corresponding votes based on the number of voters. Therefore, the election is related not only to the benefits obtained by the node but also to its comprehensive evaluation and the number of voters. If two nodes receive the same vote, the node with a higher comprehensive reputation is given priority in the ranking. For example, in an election where node A and node B each receive 1000 votes, node A’s number of stake votes is 800, its comprehensive reputation score is 50, and only four nodes vote for it. Node B’s number of stake votes is 600, its comprehensive reputation score is 80, and it receives votes from five nodes. In this situation, if only one leader node position remains, B will be selected as the leader node. Displayed in descending order of priority as comprehensive credit rating, number of voters, and stake votes, this approach aims to solve the problem of node misconduct at its root by democratizing the process and subjecting leader nodes to constraints, thereby safeguarding the fundamental interests of the vast majority of nodes.
Comprehensive reputation evaluation
This paper argues that the election process of the DPoS consensus mechanism is too simplistic, as it considers only the number of election votes that a node receives. This approach fails to comprehensively reflect the node’s actual capabilities and does not consider the voters’ election preferences. As a result, nodes with a significant stake often win and become leader nodes. To address this issue, the comprehensive reputation evaluation score is normalized considering various attributes of the nodes. The scoring results are shown in Table 3.
Table 3 Comprehensive reputation evaluation.
Since some of the evaluation indicators in Table 3 are continuous while others are discrete, different normalization methods need to be employed to obtain corresponding scores for different indicators. The continuous indicators include the number of transactions/people, wealth balance, network latency, network jitter, and network bandwidth, while the discrete indicators include the number of violations, the number of successful elections, and the number of votes. The value range of the indicator “number of transactions/people” is (0,1), and the value range of the other indicators is (0, + ∞). The equation for calculating the “number of transactions/people” is set as shown in Eq. (1).
$$A_{1} = \left\{ {\begin{array}{*{20}l} {0,} \hfill & {{\text{G}} = 0} \hfill \\ {\frac{{\text{N}}}{{\text{G}}}*10,} \hfill & {{\text{G}} > 0} \hfill \\ \end{array} } \right.$$
(1)
where N represents the number of transactional nodes and G represents the number of transactions. It reflects the degree of connection between the node and other nodes. Generally, nodes that transact with many others are safer than those with a large number of transactions with only a few nodes. The limit value of each item, denoted by x, is determined based on the situation and falls within the specified range, as shown in Eq. (2). The wealth balance and network bandwidth indicators use the same function to set their respective values.
$${A}_{i}=20*\left(\frac{1}{1+{e}^{-{a}_{i}x}}-0.5\right)$$
(2)
where x indicates the value of this item and expresses the limit value.
In Eq. (3), x represents the limited value of this indicator. The lower the network latency and network jitter are, the higher the score will be.
The last indicators, which are the number of violations, the number of elections, and the number of votes, are discrete values and are assigned different scores according to their respective ranges. The scores corresponding to each count are shown in Table 4.
$$A_{3} = \left\{ {\begin{array}{*{20}l} {10*\cos \frac{\pi }{200}x,} \hfill & {0 \le x \le 100} \hfill \\ {0,} \hfill & {x > 100} \hfill \\ \end{array} } \right.$$
(3)
Table 4 Score conversion.
The reputation evaluation mechanism proposed in this paper comprehensively considers three aspects of nodes, wealth level, node performance, and stability, to calculate their scores. Moreover, the scores obtain the present data based on historical records. Each node is set as an M × N dimensional matrix, where M represents M times the reputation evaluation score and N represents N dimensions of reputation evaluation (M < = N), as shown in Eq. (4).
$${\text{N}} = \left( {\begin{array}{*{20}c} {a_{11} } & \cdots & {a_{1n} } \\ \vdots & \ddots & \vdots \\ {a_{m1} } & \cdots & {a_{mn} } \\ \end{array} } \right)$$
(4)
The comprehensive reputation rating is a combined concept related to three dimensions. The rating is set after rating each aspect of the node. The weight w and the matrix l are not fixed. They are also transformed into matrix states as the position of the node in the system changes. The result of the rating is set as the output using Eq. (5).
$$\text{T}=\text{lN}{w}^{T}=\left({l}_{1}\dots {\text{l}}_{\text{m}}\right)\left(\begin{array}{ccc}{a}_{11}& \cdots & {a}_{1n}\\ \vdots & \ddots & \vdots \\ {a}_{m1}& \cdots & {a}_{mn}\end{array}\right){\left({w}_{1}\dots {w}_{n}\right)}^{T}$$
(5)
Here, T represents the comprehensive reputation score, and l and w represent the correlation coefficient. Because l is a matrix of order 1*M, M is the number of times in historical records, and M < = N is set, the number of dimensions of l is uncertain. Set the term l above to add up to 1, which is l1 + l2 + …… + ln = 1; w is also a one-dimensional matrix whose dimension is N*1, and its purpose is to act as a weight; within a certain period of time, w is a fixed matrix, and w will not change until the system changes the basic settings.
Assume that a node conducts its first comprehensive reputation rating, with no previous transaction volume, violations, elections or vote. The initial wealth of the node is 10, the latency is 50 ms, the jitter is 100 ms, and the network bandwidth is 100 M. According to the equation, the node’s comprehensive reputation rating is 41.55. This score is relatively good at the beginning and gradually increases as the patient participates in system activities continuously.
Voting calculation method
To ensure the security and stability of the blockchain system, this paper combines the comprehensive reputation score with voting and randomly sorts the blocks, as shown in Eqs. (3–6).
$$Z=\sum_{i=1}^{n}{X}_{i}+nT$$
(6)
where Z represents the final election score, Xi represents the voting rights earned by the node, n is the number of nodes that vote for this node, and T is the comprehensive reputation score.
The voting process is divided into stake votes and reputation votes. The more reputation scores and voters there are, the more total votes that are obtained. In the early stages of blockchain operation, nodes have relatively few stakes, so the impact of reputation votes is greater than that of equity votes. This is aimed at selecting the most suitable node as the leader node in the early stage. As an operation progresses, the role of equity votes becomes increasingly important, and corresponding mechanisms need to be established to regulate it. The election vote algorithm used in this paper is shown in Table 5.
Table 5 Election vote counting algorithm.
This paper argues that the election process utilized by the original DPoS consensus mechanism is overly simplistic, as it relies solely on the vote count to select the node that will oversee the entire blockchain. This approach cannot ensure the security and stability of the voting process, and if a malicious node behaves improperly during an election, it can pose a significant threat to the stability and security of the system as well as the safety of other nodes’ assets. Therefore, this paper proposes a different approach to the election process of the DPoS consensus mechanism by increasing the complexity of the process. We set up a threshold and optimized the vote-counting process to enhance the security and stability of the election. The specific performance of the proposed method was verified through experiments.
The election cycle in this paper can be customized, but it requires the agreement of the blockchain committee and general nodes. The election cycle includes four steps: node self-recommendation, calculating the comprehensive reputation score, voting, and replacing the new leader. Election is conducted only among general nodes without affecting the production or verification processes of leader nodes or follower nodes. Nodes start voting for preferred nodes. If they have no preference, they can use the LINK mechanism to collaborate with other nodes and gain additional rewards.
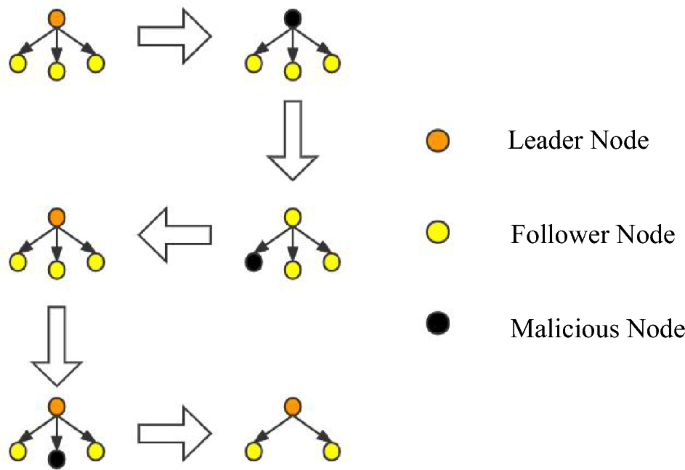
View changes
During the consensus process, conducting a large number of updates is not in line with the system’s interests, as the leader node (LN) and follower node (FN) on each node have already been established. Therefore, it is crucial to handle problematic nodes accurately when issues arise with either the LN or FN. For instance, when a node fails to perform its duties for an extended period or frequently fails to produce or verify blocks within the specified time range due to latency, the system will precisely handle them. For leader nodes, if they engage in malicious behavior such as producing blocks out of order, the behavior is recorded, and their identity as a leader node is downgraded to a follower node. The follower node inherits the leader node’s position, and the nature of their work is transformed as they swap their responsibilities of producing and verifying blocks with their original work. This type of behavior will not significantly affect the operation of the blockchain system. Instead of waiting until the end of the current committee round to punish malicious nodes, dynamic punishment is imposed on the nodes that affect the operation of the blockchain system to maintain system security. The view change operation is illustrated in Fig. 4.
In traditional PBFT, view changes are performed according to the view change protocol by changing the view number V to the next view number V + 1. During this process, nodes only receive view change messages and no other messages from other nodes. In this paper, the leader node group (LN) and follower node group (FN) are selected through an election of the LINK group. The node with LINKi[0] is added to the LN leader node group, while the other three LINK groups’ follower nodes join the FN follower node group since it is a configuration pattern of one master and three slaves. The view change in this paper requires only rearranging the node order within the LINK group to easily remove malicious nodes. Afterward, the change is broadcast to other committee nodes, and during the view transition, the LINK group does not receive block production or verification commands from the committee for stability reasons until the transition is completed.
News
The Hype Around Blockchain Mortgage Has Died Down, But This CEO Still Believes

LiquidFi Founder Ian Ferreira Sees Huge Potential in Blockchain Despite Hype around technology is dead.
“Blockchain technology has been a buzzword for a long time, and it shouldn’t be,” Ferriera said. “It should be a technology that lives in the background, but it makes everything much more efficient, much more transparent, and ultimately it saves costs for everyone. That’s the goal.”
Before founding his firm, Ferriera was a portfolio manager at a hedge fund, a job that ended up revealing “interesting intricacies” related to the mortgage industry.
Being a mortgage trader opened Ferriera’s eyes to a lot of the operational and infrastructure problems that needed to be solved in the mortgage-backed securities industry, he said. That later led to the birth of LiquidFi.
“The point of what we do is to get raw data attached to a resource [a loan] on a blockchain so that it’s provable. You reduce that trust problem because you have the data, you have the document associated with that data,” said the LiquidFi CEO.
Ferriera spoke with National Mortgage News about the value of blockchain technology, why blockchain hype has fizzled out, and why it shouldn’t.
News
New bill pushes Department of Veterans Affairs to examine how blockchain can improve its work

The Department of Veterans Affairs would have to evaluate how blockchain technology could be used to improve benefits and services offered to veterans, according to a legislative proposal introduced Tuesday.
The bill, sponsored by Rep. Nancy Mace, R-S.C., would direct the VA to “conduct a comprehensive study of the feasibility, potential benefits, and risks associated with using distributed ledger technology in various programs and services.”
Distributed ledger technology, including blockchain, is used to protect and track information by storing data across multiple computers and keeping a record of its use.
According to the text of the legislation, which Mace’s office shared exclusively with Nextgov/FCW ahead of its publication, blockchain “could significantly improve benefits allocation, insurance program management, and recordkeeping within the Department of Veterans Affairs.”
“We need to bring the federal government into the 21st century,” Mace said in a statement. “This bill will open the door to research on improving outdated systems that fail our veterans because we owe it to them to use every tool at our disposal to improve their lives.”
Within one year of the law taking effect, the Department of Veterans Affairs will be required to submit a report to the House and Senate Veterans Affairs committees detailing its findings, as well as the benefits and risks identified in using the technology.
The mandatory review is expected to include information on how the department’s use of blockchain could improve the way benefits decisions are administered, improve the management and security of veterans’ personal data, streamline the insurance claims process, and “increase transparency and accountability in service delivery.”
The Department of Veterans Affairs has been studying the potential benefits of using distributed ledger technology, with the department emission a request for information in November 2021 seeking input from contractors on how blockchain could be leveraged, in part, to streamline its supply chains and “secure data sharing between institutions.”
The VA’s National Institute of Artificial Intelligence has also valued the use of blockchain, with three of the use cases tested during the 2021 AI tech sprint focused on examining its capabilities.
Mace previously introduced a May bill that would direct Customs and Border Protection to create a public blockchain platform to store and share data collected at U.S. borders.
Lawmakers also proposed additional measures that would push the Department of Veterans Affairs to consider adopting other modernized technologies to improve veteran services.
Rep. David Valadao, R-Calif., introduced legislation in June that would have directed the department to report to lawmakers on how it plans to expand the use of “certain automation tools” to process veterans’ claims. The House of Representatives Subcommittee on Disability Assistance and Memorial Affairs gave a favorable hearing on the congressman’s bill during a Markup of July 23.
News
California DMV Uses Blockchain to Fight Auto Title Fraud

TDR’s Three Takeaways: California DMV Uses Blockchain to Fight Fraud
- California DMV uses blockchain technology to manage 42 million auto titles.
- The initiative aims to improve safety and reduce car title fraud.
- The immutable nature of blockchain ensures accurate and tamper-proof records.
The California Department of Motor Vehicles (DMV) is implementing blockchain technology to manage and secure 42 million auto titles. This innovative move aims to address and reduce the persistent problem of auto title fraud, a problem that costs consumers and the industry millions of dollars each year. By moving to a blockchain-based system, the DMV is taking advantage of the technology’s key feature: immutability.
Blockchain, a decentralized ledger technology, ensures that once a car title is registered, it cannot be altered or tampered with. This creates a highly secure and transparent system, significantly reducing the risk of fraudulent activity. Every transaction and update made to a car title is permanently recorded on the blockchain, providing a complete and immutable history of the vehicle’s ownership and status.
As first reported by Reuters, the DMV’s adoption of blockchain isn’t just about preventing fraud. It’s also aimed at streamlining the auto title process, making it more efficient and intuitive. Traditional auto title processing involves a lot of paperwork and manual verification, which can be time-consuming and prone to human error. Blockchain technology automates and digitizes this process, reducing the need for physical documents and minimizing the chances of errors.
Additionally, blockchain enables faster verification and transfer of car titles. For example, when a car is sold, the transfer of ownership can be done almost instantly on the blockchain, compared to days or even weeks in the conventional system. This speed and efficiency can benefit both the DMV and the vehicle owners.
The California DMV’s move is part of a broader trend of government agencies exploring blockchain technology to improve their services. By adopting this technology, the DMV is setting a precedent for other states and industries to follow, showcasing blockchain’s potential to improve safety and efficiency in public services.
-

 Ethereum12 months ago
Ethereum12 months agoEthereum Posts First Consecutive Monthly Losses Since August 2023 on New ETFs
-

 Regulation12 months ago
Regulation12 months agoCryptocurrency Regulation in Slovenia 2024
-

 News12 months ago
News12 months agoNew bill pushes Department of Veterans Affairs to examine how blockchain can improve its work
-

 Regulation12 months ago
Regulation12 months agoThink You Own Your Crypto? New UK Law Would Ensure It – DL News
-

 Regulation12 months ago
Regulation12 months agoUpbit, Coinone, Bithumb Face New Fees Under South Korea’s Cryptocurrency Law
-
 Regulation12 months ago
Regulation12 months agoA Blank Slate for Cryptocurrencies: Kamala Harris’ Regulatory Opportunity
-

 Regulation12 months ago
Regulation12 months agoBahamas Passes Cryptocurrency Bill Designed to Prevent FTX, Terra Disasters
-

 Regulation12 months ago
Regulation12 months agoIndia to Follow G20 Policy for Cryptocurrency Regulation: MoS Finance
-

 News1 year ago
News1 year ago“Captain Tsubasa – RIVALS” launches on Oasys Blockchain
-

 Ethereum1 year ago
Ethereum1 year agoComment deux frères auraient dérobé 25 millions de dollars lors d’un braquage d’Ethereum de 12 secondes • The Register
-

 News12 months ago
News12 months agoEU supports 15 startups to fight online disinformation with blockchain
-

 News1 year ago
News1 year agoSolana ranks the fastest blockchain in the world, surpassing Ethereum, Polygon ⋆ ZyCrypto